Secure Research Data Management: Designing a Protected Online Platform for Academic and Institutional Research
Table of Contents
- Secure Research Data Management: Designing a Protected Online Platform for Academic and Institutional Research
- Why Secure Research Data Management Matters
- Core Objectives of the Platform
- System Architecture Overview
- Frontend Design: Usability Meets Security
- Backend Architecture: The Core Engine
- Database Design and Data Structuring
- Security Framework: Protecting Sensitive Data
- 1. Confidentiality Through Encryption
- 2. Integrity Through Validation and Logging
- 3. Availability Through Backup Systems
- Role-Based Access Control (RBAC)
- Version Control and Research Lifecycle Management
- Collaboration and Workflow Features
- Compliance and Ethical Considerations
- Cloud Integration and Scalability
- AI Integration Opportunities
- Challenges in System Development
- Data Sensitivity
- Performance Optimization
- User Adoption
- Continuous Security Updates
- Benefits to Academic Institutions
- Academic and IT Project Value
- Future Enhancements
- Conclusion
Research is built on data. Whether it is a thesis manuscript, survey dataset, laboratory result, or institutional research output, information is the foundation of academic progress. Yet in many institutions, research data is still stored in fragmented ways—USB drives, personal laptops, email attachments, or unsecured cloud folders.
This approach creates serious risks: data breaches, accidental deletion, version confusion, and even intellectual property theft.
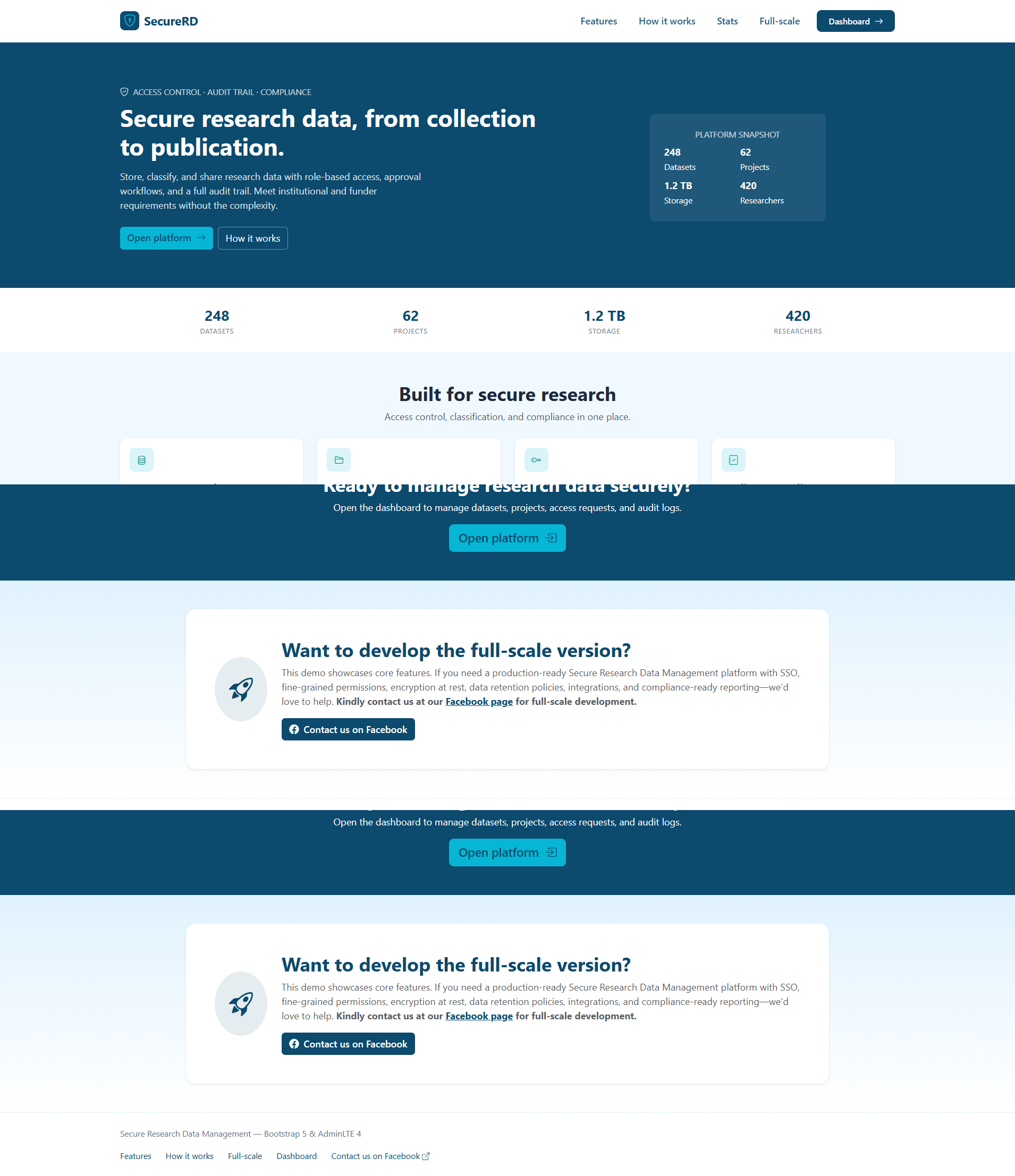
The solution lies in building a Secure Research Data Management (SRDM) platform—a centralized, web-based system designed to store, organize, protect, and manage research data throughout its lifecycle. This is not merely a file storage website. It is a structured, secure digital ecosystem engineered with cybersecurity principles, database integrity, and role-based access control.
From an IT perspective, this project demonstrates how web development, encryption technologies, and access governance can be combined into a robust research infrastructure.
Why Secure Research Data Management Matters
Research data is valuable for several reasons:
- It represents intellectual effort and innovation.
- It may contain confidential participant information.
- It supports institutional credibility.
- It is often required for accreditation and compliance.
When research data is poorly managed, institutions face:
- Data loss due to hardware failure
- Unauthorized access
- Plagiarism or data manipulation
- Difficulty retrieving past research outputs
- Non-compliance with regulatory standards
A secure online platform solves these issues by centralizing and protecting research assets.
Core Objectives of the Platform
The Secure Research Data Management system is designed to:
- Provide centralized storage for research documents and datasets.
- Ensure data confidentiality, integrity, and availability.
- Implement controlled access based on user roles.
- Maintain audit logs for accountability.
- Support version control and data lifecycle management.
- Enable secure collaboration among researchers.
This framework ensures that research data is not only accessible but also protected.
System Architecture Overview
A well-designed SRDM platform follows a layered architecture:
- Frontend (User Interface)
- Backend (Application Logic)
- Database Layer
- Security and Encryption Layer
- Cloud or Server Infrastructure
Each layer must be engineered carefully to ensure security and performance.
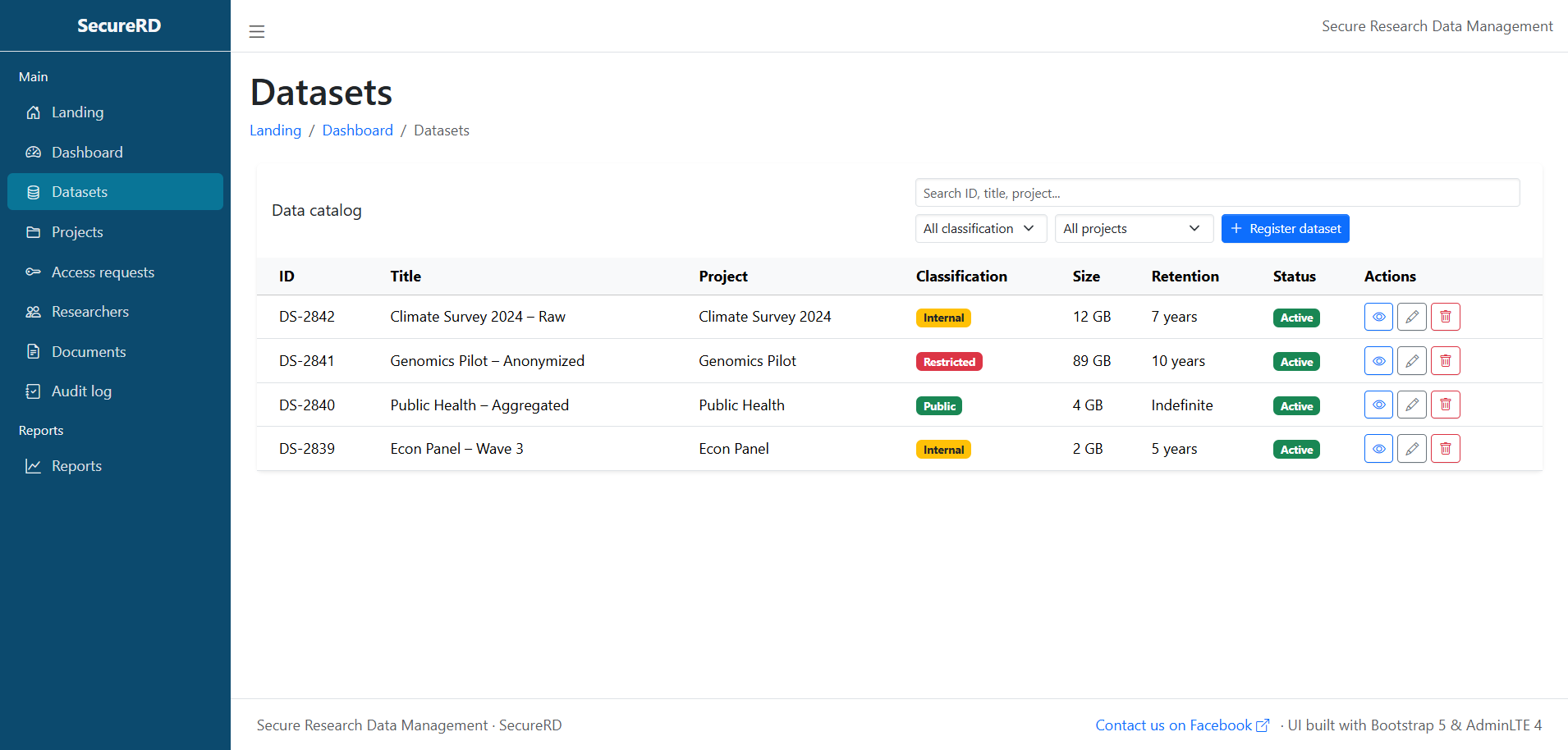
Frontend Design: Usability Meets Security
The user interface should be simple, clean, and intuitive. Researchers are not always technical experts; therefore, the platform must avoid unnecessary complexity.
Frontend technologies may include:
- HTML5 for page structure
- CSS3 or Bootstrap for responsive design
- JavaScript for dynamic features
- AJAX for asynchronous file uploads
The interface should provide:
- Dashboard overview
- Project folder structure
- Upload and download controls
- Access management settings
- Activity history
A well-organized dashboard enhances productivity and reduces confusion.
Backend Architecture: The Core Engine
The backend is responsible for processing requests, enforcing rules, and maintaining security.
Technologies may include:
- PHP (native or MVC framework)
- Node.js
- Python-based frameworks
- RESTful API design
The backend handles:
- User authentication
- Role-based access control (RBAC)
- File encryption and decryption
- Database transactions
- Audit trail logging
- Notification services
A modular design improves maintainability and scalability.
Database Design and Data Structuring
A relational database such as MySQL or PostgreSQL can be used to manage structured information.
Key tables may include:
- Users
- Roles
- ResearchProjects
- Files
- AccessPermissions
- AuditLogs
- VersionHistory
Normalization principles should be applied to avoid redundancy and ensure data integrity.
Indexing critical fields—such as project IDs and user roles—improves performance when handling large datasets.
Security Framework: Protecting Sensitive Data
Security is the backbone of this system. The platform must adhere to the core cybersecurity principles known as the CIA Triad:
- Confidentiality
- Integrity
- Availability
1. Confidentiality Through Encryption
Data must be encrypted:
- In transit (using HTTPS/SSL)
- At rest (using AES-based encryption methods)
Even if a database breach occurs, encrypted files cannot be easily accessed without proper keys.
Password hashing techniques such as bcrypt should be used instead of plain-text storage.
2. Integrity Through Validation and Logging
To maintain data integrity:
- Input validation prevents injection attacks.
- File checksum verification ensures files are not corrupted.
- Audit logs record every modification.
An audit log may track:
- Who uploaded a file
- Who modified a dataset
- Who accessed sensitive information
- Timestamp of actions
This creates accountability and traceability.
3. Availability Through Backup Systems
Data must remain accessible even during system failures.
Strategies include:
- Automated daily backups
- Redundant storage systems
- Cloud-based disaster recovery solutions
- Failover server configurations
Availability ensures research continuity.
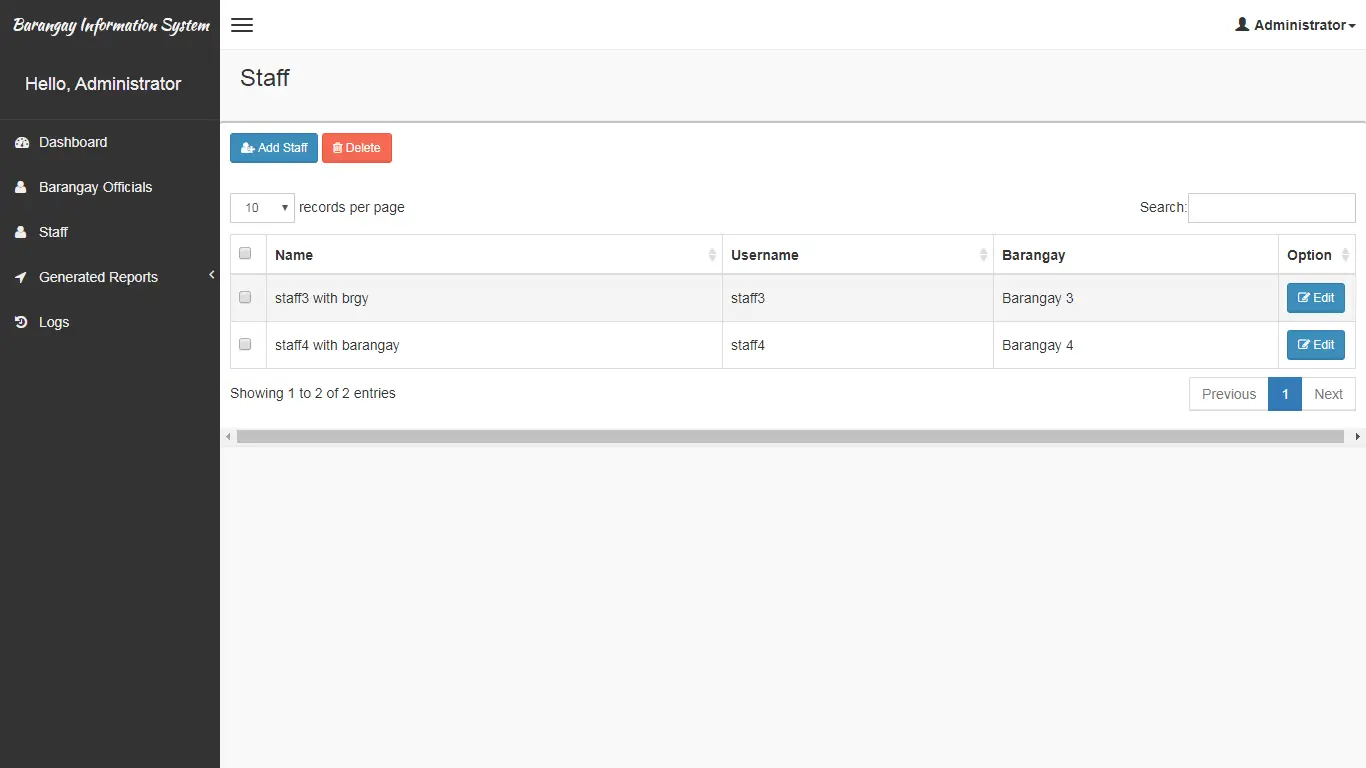
Role-Based Access Control (RBAC)
Not all users should have the same permissions.
The platform may define roles such as:
- Administrator
- Research Director
- Faculty Researcher
- Student Researcher
- External Collaborator
- Reviewer
Each role has specific privileges.
For example:
- Only administrators can delete projects.
- Researchers can upload and edit their own files.
- Reviewers may only view certain documents.
RBAC prevents unauthorized access and accidental data exposure.
Version Control and Research Lifecycle Management
Research evolves over time. Multiple drafts and datasets may exist.
The platform should:
- Automatically create version histories.
- Allow rollback to previous versions.
- Display modification timelines.
- Prevent accidental overwriting.
This ensures clarity and prevents confusion between file versions.
Collaboration and Workflow Features
Modern research often involves collaboration.
The platform can include:
- Shared project workspaces
- Permission-based file sharing
- Commenting systems
- Approval workflows
- Submission and review tracking
These features transform the system into a research management ecosystem rather than simple storage.
Compliance and Ethical Considerations
Research involving human participants requires strict confidentiality.
The system should comply with:
- Data privacy regulations
- Institutional research policies
- Ethical review board standards
Access to sensitive data must be limited and logged.
Additionally, consent forms and ethical approval documents can be stored securely within project folders.
Cloud Integration and Scalability
Cloud-based deployment offers advantages such as:
- Elastic storage capacity
- High availability
- Geographic redundancy
- Automatic scaling
Cloud providers can support:
- Virtual private servers
- Object storage systems
- Managed database services
This makes the platform adaptable to growing institutional needs.
AI Integration Opportunities
Advanced versions of the platform may integrate AI features such as:
- Automated document classification
- Plagiarism detection
- Research keyword extraction
- Metadata tagging
- Data anomaly detection
AI can assist researchers in organizing and analyzing data more efficiently.
Challenges in System Development
Designing a secure research platform is not without obstacles.
Data Sensitivity
Handling confidential research data requires extreme caution. Even small misconfigurations can lead to breaches.
Performance Optimization
Large datasets and file uploads can strain server resources. Efficient caching and optimized queries are necessary.
User Adoption
Researchers accustomed to traditional storage methods may resist new systems. Proper training and onboarding are essential.
Continuous Security Updates
Cybersecurity threats evolve. The platform must:
- Regularly update software components
- Patch vulnerabilities
- Conduct penetration testing
Security is not a one-time implementation—it is ongoing maintenance.
Benefits to Academic Institutions
A Secure Research Data Management platform provides:
- Centralized research repository
- Improved institutional transparency
- Better compliance documentation
- Increased research credibility
- Enhanced collaboration opportunities
Administrators gain visibility into research productivity, while researchers benefit from organized and protected storage.
Academic and IT Project Value
From a technical standpoint, this system integrates:
- Web development
- Database management
- Encryption methods
- Access control mechanisms
- Cloud deployment strategies
It serves as an excellent IT capstone project or enterprise-level system prototype.
It demonstrates the practical application of cybersecurity principles in a real-world academic context.
Future Enhancements
The platform can expand to include:
- Blockchain-based research timestamping
- Integration with journal submission systems
- Automated grant tracking
- Research analytics dashboards
- Multi-institution collaboration modules
These enhancements would further strengthen its role in digital research infrastructure.
Conclusion
Secure Research Data Management is no longer optional in modern academic institutions. As research output increases and digital storage becomes the norm, centralized and secure systems are essential for protecting intellectual property and maintaining compliance.
By combining robust backend development, structured database architecture, encryption technologies, and role-based access control, the Secure Research Data Management platform offers a comprehensive solution to modern research challenges.
This project reflects the broader evolution of IT systems—from simple storage tools to intelligent, secure, and collaborative digital ecosystems. When properly designed and maintained, such a platform does more than protect data. It supports innovation, safeguards academic integrity, and ensures that valuable research remains secure for years to come.
You may visit our Facebook page for more information, inquiries, and comments. Please subscribe also to our YouTube Channel to receive free capstone projects resources and computer programming tutorials.
Hire our team to do the project.